We have covered several methods that cybercriminals use to get your information or your money. Hopefully, you have learned a lot and taken steps to make your online presence more secure. However, there is more to cybersecurity than just protecting yourself. Cyber-champions actively help others around them avoid traps set by cyber-thieves. Cyber-champions are valuable
Tag: information security
Do your part. Examining role-based cybersecurity threats.

Cybersecurity attacks are personal. Cybercriminals steal personal information and target their victims based on their role and what information they have access to. Here are some tips that every redbird should know based on their roles and responsibilities. Students Students are often targeted with fear tactics or opportunity tactics. Either way the goal is to get
Don’t take the bait. Phishing attempts are on the rise.
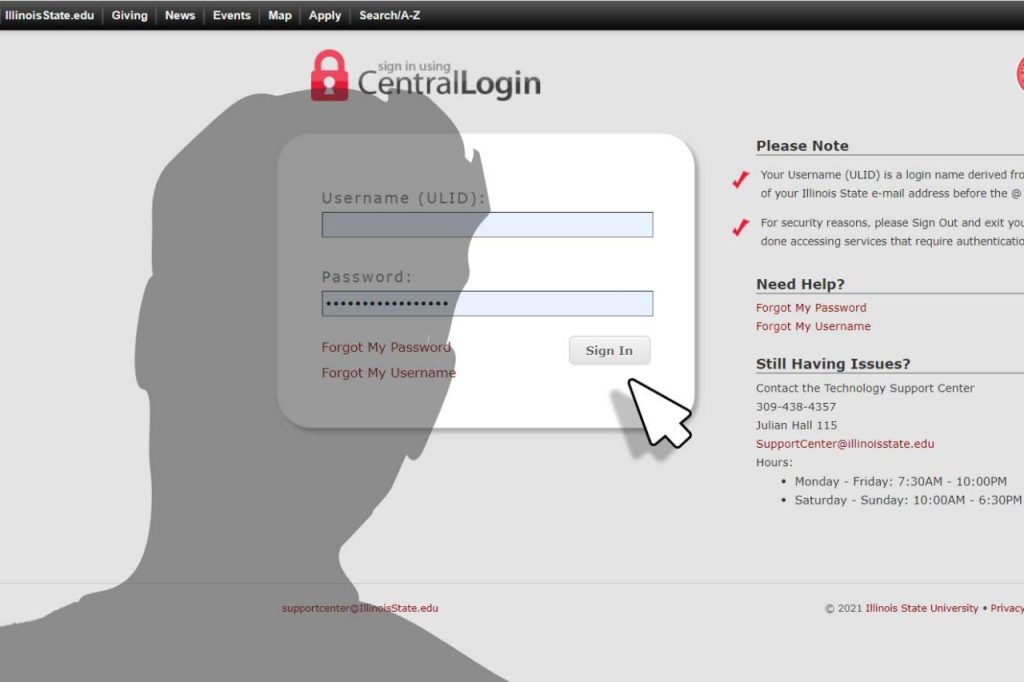
Phishing isn’t exclusive to email anymore. Scammers use text messages, DMs, phone calls, and many more methods to snag your personal information such as your ULID and password.
Illinois State meets growing need for cybersecurity professionals
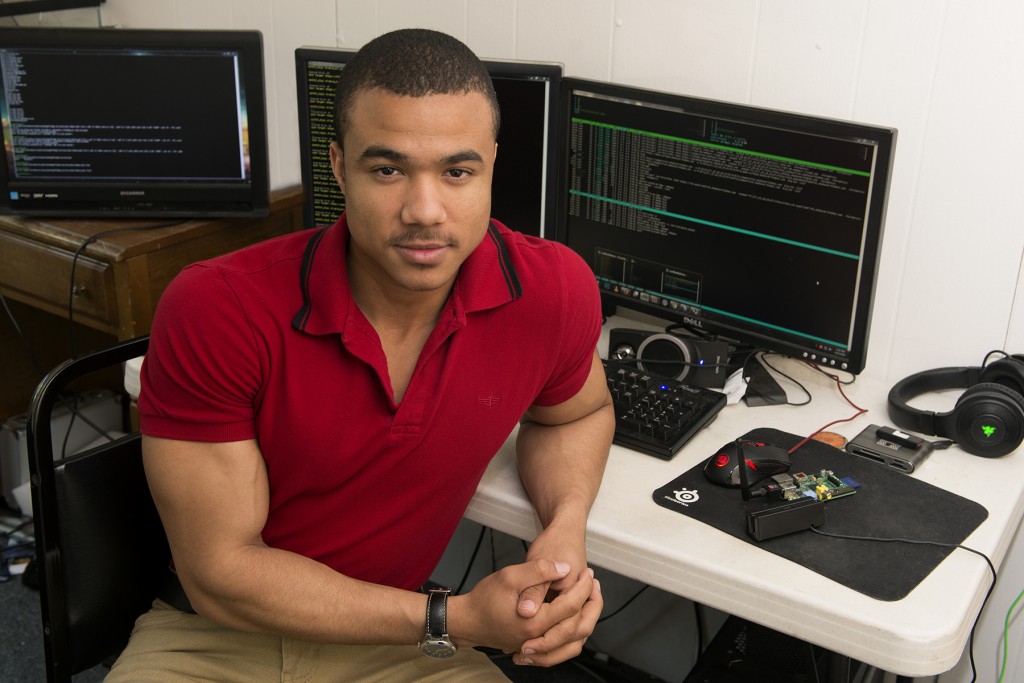
Illinois State’s School of Information Technology is a nationally recognized leader in cybersecurity education with 125 students in its rapidly growing information assurance and security sequence.
Capture the Flag tests information security skills

Students in the School of Information Technology will take part in a high-tech game of “capture the flag” beginning Friday, November 6.
